The proper management of the invite function across digital solutions ensures security
Thinking about the invitation functions of digital tools, I recall my very first birthday party as a child. To be precise, not my own, but one of my childhood friend’s, who is still my best friend. Eric had invited to his birthday – as a child, that sounds so magnificently simple.
Truth be told, behind the scenes Eric’s parents probably had to select the guest list, write and deliver invitation cards, guests had to accept or cancel, and many more things. In short, a kids’ birthday party is a time-consuming coordination process.
The invitationfunction is much more complex than expected even with collaborative solutions
Let’s travel to the year 2021 – a transport planner at (fictitious) Eric Ltd., a medium-sized mechanical engineering company, wants to involve his forwarding agents in the time slot planning of outbound shipments. This is not to be done via calendar, lists, e-mail and fax, as is customary, but via an integrated planning calendar, which allows more automation in the monitoring of secondary conditions as would be the case in a simple calendar tool. The forwarder should also bring in his telematics, of course only those that concern any transports at Eric Ltd.
The transport planner works using a tool, for instance a time slot management system for loading processes based on SAP, which is running on-premise behind the company’s own firewall. Unsuspecting of this, he presents his request to the internal IT department, which explains to him that such releases are subject to IT compliance guidelines and that the tool in question has not yet been approved for external access, meaning that access trough the demilitarized zone (DMZ) would be necessary. In addition, the creation of new users must first go through the master user creation process and must be cleared by Identity Management.
Great frustration on all sides ensues. The freight forwarder has relatively little to gain from a lengthy registration process – the time spent here is perhaps better invested in the orderly dispatching of his own fleet. The dispatcher deems it all too much effort for this service provider and in the future will be content with lists, fax and calendar function again.
Who's invited and who´s not? digital collaboration ought to be regulated
There’s a good reason for all these policies and regulations: security. No company wants to risk unauthorized people gaining access to the corporate network or messing things up. At the very least, incidents can result in a serious loss of reputation. For this reason, access is hand-picked and highly restricted, or at least in theory it should be.
Basically, we are dealing with a fairly standard use case: The dispatcher wishes to have transparency regarding the delivery status of a shipment for the end customer so that he can answer any questions or, in the unforeseen circumstances, achieve on-time delivery nevertheless. This should work preferably with as many carriers as possible.
A software such as myleo / slot offers a minimal integration with the upstream system – to the extent necessary, but not as much as possible: for example, a simple document integration by means of a pre-planned selection process for the transport service provider (the fact that interfaces are generally not simple should be acknowledged and discussed, this however should best be the focus in a separate post).
Mamage users as the key to clean processes
In addition, the tool offers user administration and the option of extending invitations to dedicated transport service providers for deliveries, whitelisting of loading points and simple authorization control. Thus, for example, dispatchers at Eric Ltd. are allowed to schedule the pre-planning for freight carriers using fixed quotas, while the service providers are only allowed to redeem these – or optionally book vacant time slots.
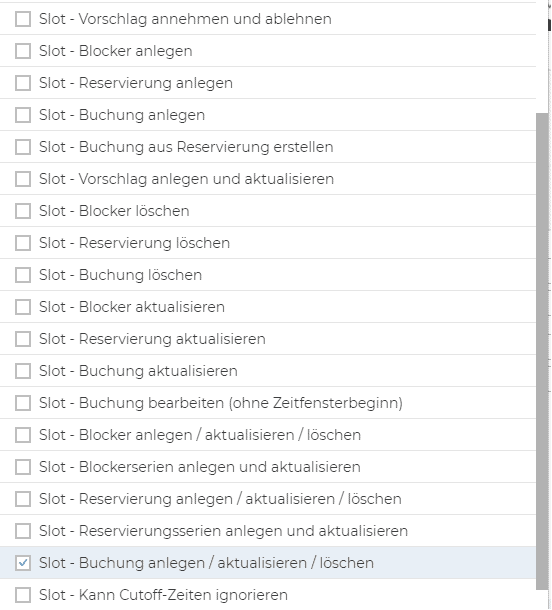
The forwarders are simply added as a master record and invited by e-mail, whereupon they can register. Subsequently, they are immediately ready to go and can do exactly what they were invited for – no more, but also no less. Any inactive users are flagged after a certain period of time and can be removed from the “guest list” if necessary, without having to delete the entire service provider account or incur additional licensing costs.
API based integration into the upstream system takes place very selectively, such as in the form of reporting the pickup time slots. This feature also takes information security into account, given that data economy is still the most powerful lever here, despite encrypted, API-based integration.
Conclusion
Collaborative processes are no kids’ party. This applies neither to the invitation of participants nor to the security requirements placed on invited guests. Selective, tightly defined integration of upstream systems, coupled with flexibility of internal end-user reference to the guest list can take collaboration with digital tools to a new level – all without conflicts arising from IT policies or lengthy onboarding of new users.
Behind every policy there must always be a corresponding security measure, especially in on-premise environments, where by definition every guest is involuntarily directly in-house.
We support you in making your operational activities more interlinked, transparent and cost-saving and thus improve your supply chains. Find out more about the quick-to-implement capabilities of our cloud-based 360° logistics platform myleo / dsc.
If you have any questions about this or any other topic on the blog, please feel free to contact us at blog@leogistics.com.
Uwe Kunath
Development Architect

